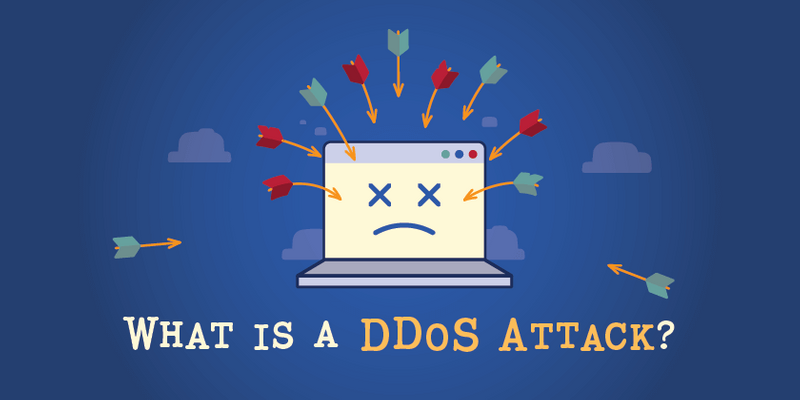
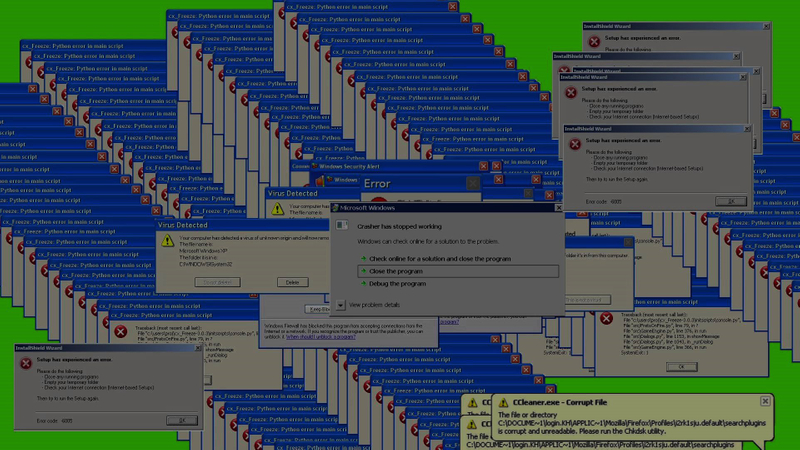
Practicing For DDOS, How do you defend against a nuclear bomb?
What we’ll attempt to do in this article is similar to testing a nuclear bomb (okay, not really). But still, there’s no way to tell exactly what will happen, other than to blast the damn thing because more often than not that’s just the way it is with DDOSing.